A pair of high-profile security incidents over April 18–19 has rattled both decentralized finance and mainstream cloud infrastructure, underscoring a growing reality: as AI accelerates software creation, it is also accelerating the pace and sophistication of attacks—and the blast radius increasingly extends beyond smart contracts to the tools and services surrounding them.
On April 18 UTC, KelpDAO’s LayerZero-based cross-chain bridge was exploited, with an attacker siphoning roughly 116,500 rsETH—valued at about $292 million—within 46 minutes, according to figures cited in the Korean report. The stolen assets were quickly posted as collateral on Aave (AAVE) to borrow native Ether, a maneuver that amplified market stress by turning bridged exposure into immediate on-chain liquidity.
Aave moved into an emergency freeze, triggering a broader DeFi shock. Total value locked (TVL) on Aave reportedly fell by about $6.6 billion, while AAVE dropped as much as 16% amid a rush to de-risk. The pullback spread quickly across protocols as users rushed to withdraw funds, with total outflows across DeFi estimated at around $10 billion—behavior reminiscent of a digital ‘bank run’ driven by confidence rather than solvency.
The following day, April 19 UTC, attention shifted from smart contracts to the web layer. Cloud platform Vercel—widely used for hosting front ends and dashboards—was breached via a third-party AI tool, Context.ai, used by an employee. The attacker allegedly used that foothold to seize access to a Google account and then move deeper into internal infrastructure. A post on a hacking forum claimed internal databases, employee accounts, and GitHub and NPM tokens were being offered for $2 million, the report said.
For crypto teams, the Vercel incident carried an especially sharp lesson: the blockchain can remain intact while the user experience layer fails catastrophically. Smart contracts may continue to execute as designed, but compromised front ends can redirect transactions, steal credentials, or manipulate what users sign. In effect, the ‘lock’ may still work—while the front door is left open.
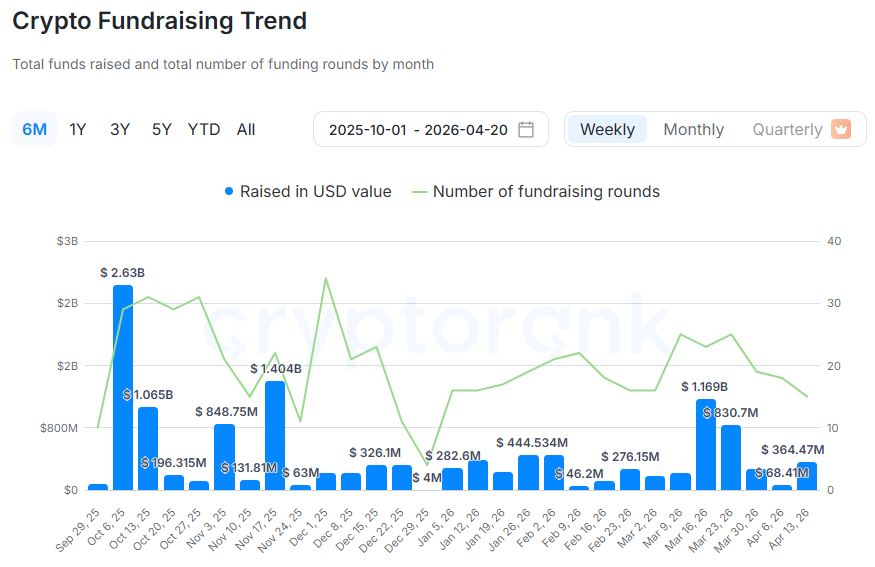
The incidents also fit into a wider pattern. The Korean commentary pointed to a string of April exploits—ranging from Drift Protocol to CoW Swap, Zerion, Rhea Finance, and Silo Finance—and said 2026 year-to-date DeFi losses had already surpassed $450 million across 45 protocols by mid-April. The takeaway is less about any single bug than about a structural change: attacks are becoming more frequent, more targeted, and faster to execute, shrinking the window for detection and response.
Industry warnings are growing louder. Ledger’s CTO was quoted as saying 2026 could become the worst year on record for hacking losses. While such statements are inherently speculative, the sequence of events illustrates why security teams are increasingly focused on systemic risk—bridges, shared libraries, cloud services, identity providers, and AI-enabled workflows—rather than isolated protocol code.
At the center of the shift is AI itself. Anthropic CEO Dario Amodei has argued that AI could be writing the majority of code within months, and the broader market is already moving in that direction through copilots, agents, and automated deployment tools. The same capabilities that lower barriers to launching services—rapid code generation, dependency selection, and automated configuration—also lower barriers to offense, enabling faster vulnerability discovery, exploit construction, and social engineering at scale.
The report cited internal testing of a recent Anthropic model that allegedly identified thousands of previously unknown vulnerabilities, including a flaw in a 27-year-old operating system component, and achieved a 72.4% success rate generating effective exploit code—far above earlier models. Even if such figures vary by benchmark and environment, the direction is clear: AI is compressing the attacker’s workflow from weeks to hours, while patch cycles, audits, and infrastructure modernization remain comparatively slow.
Vercel’s breach, in particular, highlights a ‘new grammar’ of attacks—one that targets the connective tissue of modern development rather than a single codebase. The weak link was not necessarily Vercel’s core product but an ecosystem of AI productivity tools, third-party OAuth relationships, and everyday employee accounts. In DeFi, the KelpDAO exploit similarly points to risk emerging at the seams—how components are connected, how trust assumptions stack, and how quickly attackers can pivot from one layer to the next.
The implications extend beyond any one region. Korean exchanges, financial institutions, and blockchain projects rely on the same global cloud providers, the same Linux-based infrastructure, and many of the same AI-enabled tools being adopted worldwide. Vulnerabilities do not respect borders, and dependence on shared platforms can turn a single compromised account or token into a multi-tenant event affecting many downstream services.
For markets, the recent events reinforce a familiar but evolving conclusion: security risk is no longer confined to smart contract code. The next phase of crypto security will be increasingly shaped by ‘identity,’ ‘front-end integrity,’ and ‘supply-chain trust’—and by how quickly defenders can adapt processes to match the speed of AI-assisted attackers. The April incidents did not just expose bugs; they exposed a widening mismatch between modern composable systems and legacy assumptions about where security boundaries begin and end.






















Comment 0