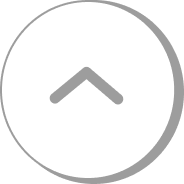
Fears that quantum computing could one day crack Bitcoin’s cryptography are resurfacing—this time with a sharper technical edge. A new research paper from Google’s Quantum AI team argues that key components of widely used elliptic curve cryptography (ECC) could, under advanced conditions, be broken far more efficiently than previously assumed, accelerating industry debate from “is this real?” to “how fast do we need to move?”
The report, released in recent days, centers on the security model underpinning Bitcoin (BTC) wallets and much of modern digital authentication. ECC is designed so that deriving a private key from a public key is computationally infeasible for classical computers. Google’s work revisits that assumption in a quantum setting, outlining models in which an attacker with sufficiently capable quantum hardware and optimized algorithms could reduce the time required to reverse-engineer keys—potentially to minutes in certain scenarios.
That does not mean Bitcoin is facing an immediate, existential hack. Current quantum computers remain well short of the scale and error-correction performance required to threaten real-world ECC deployments. Still, researchers and security engineers say the more meaningful signal is that the gap between theoretical vulnerability and practical capability appears to be narrowing. In other words, the ‘timeline risk’ is changing.
Google has already set 2029 as an internal target for migrating its own systems toward ‘post-quantum cryptography’ (PQC), a class of algorithms designed to resist quantum attacks. U.S. agencies and major technology firms have been moving in the same direction, reflecting a broader security consensus: even if the threat is not imminent, the lead time for upgrading critical infrastructure is long.
Bitcoin’s exposure, analysts note, is not a generic “crypto problem” so much as a specific architectural and governance challenge. A significant portion of the Bitcoin supply is held in addresses where the public key has already been revealed on-chain. Independent estimates cited in industry discussions suggest roughly 6.7 million BTC could be exposed under various quantum attack models, especially in older address formats where the public key can be permanently visible on the blockchain.
More immediate than dormant on-chain balances is what developers sometimes call the transaction ‘window of exposure.’ When a Bitcoin transaction is broadcast to the network, the public key may be observable until the transaction is confirmed in a block—typically minutes, sometimes longer depending on network conditions. Google’s paper discusses scenarios in which a sufficiently advanced quantum adversary could use that window to infer the private key and attempt to reroute funds before confirmation, effectively racing the mining process. While highly theoretical given today’s hardware limits, the framing has pushed parts of the developer community toward treating the issue as an engineering timeline rather than a distant abstraction.
Not everyone in the industry sees the renewed attention as proportionate. Binance founder Changpeng Zhao has publicly downplayed the latest round of concern as overblown, arguing that most cryptographic systems, including Bitcoin, can migrate to quantum-resistant schemes. Technically, that is broadly true: cryptography can be upgraded, and PQC standards are advancing. The obstacle is not the concept of migration—it is execution in a decentralized environment.
Unlike a large bank that can mandate an overnight patch across centrally managed servers, Bitcoin has no single administrator. Any meaningful cryptographic transition would require changes to wallet software, exchanges, custodians, mining infrastructure, and user practices—coordinated through Bitcoin’s open governance process and adopted voluntarily by a globally distributed set of stakeholders with different incentives. A draft proposal known as BIP 360, which discusses quantum-resistant transaction formats, exists in early form and has prompted experimental work, but it is widely seen as a starting point rather than a complete solution.
Security specialists caution that a full ecosystem migration could take close to a decade, particularly if it involves moving funds out of vulnerable address types and encouraging broad adoption of new signature schemes. That timeline is what makes the comparison to the Y2K scare imperfect. Y2K was a bug embedded in centralized IT systems that could be addressed through coordinated, top-down remediation. The quantum issue, by contrast, is about changes in underlying ‘math’ and the difficulty of executing a network-wide upgrade without a central authority—an instance where ‘decentralized governance’ itself can become a bottleneck.
The implications extend far beyond digital assets. The same class of cryptography protects global banking rails, payment networks, enterprise authentication, and government communications. Cybersecurity agencies and industry researchers have repeatedly warned about the ‘Store Now, Decrypt Later’ strategy, in which adversaries harvest encrypted data today with the expectation that future quantum systems could decrypt it. Even if Bitcoin is not uniquely vulnerable, it is uniquely transparent: because the ledger is public, the scale of potential exposure can be quantified, and because development is open-source, mitigation debates unfold in real time.
For now, markets appear largely unmoved. Bitcoin’s price action has not shown a clear reaction to Google’s publication, suggesting traders are treating quantum risk as low probability or distant. But security engineers point out that the most important lesson of Y2K was not that the danger was imaginary—it was that a massive, costly effort began years in advance. If major institutions are targeting 2029 for quantum-resistant transitions and Bitcoin’s own upgrade path could take roughly a decade to fully implement, the practical work of preparing for a quantum era may need to start well before the threat becomes visible on a price chart.
🔎 Market Interpretation
- Risk repriced as “timeline” rather than “possibility”: Google Quantum AI’s paper shifts discussion from whether ECC can be broken to how quickly practical capability could emerge, increasing attention to migration planning rather than near-term panic.
- Limited immediate market impact: Bitcoin price has shown no clear reaction, implying traders still view quantum attack risk as low-probability and/or far-off despite the updated efficiency framing.
- Quantifiable on-chain exposure is a unique headline risk: Because Bitcoin’s ledger is public, analysts can estimate potentially vulnerable coins (e.g., addresses with revealed public keys), which can periodically revive concern even before hardware is sufficient.
- Medium-term “trust and readiness” narrative: The more salient market variable is confidence in the ecosystem’s upgrade coordination (wallets/exchanges/miners/users), not current quantum hardware capability.
💡 Strategic Points
- What Google’s paper implies: Under advanced quantum conditions and optimized approaches, breaking key parts of ECC could take dramatically less time than prior assumptions—potentially fast enough to matter within a transaction confirmation window in worst-case scenarios.
- Why this is not an immediate Bitcoin-doomsday event: Today’s quantum computers lack the required scale and error correction to threaten real-world ECC at Bitcoin’s parameters, but the perceived gap between theory and practice is narrowing.
- Bitcoin-specific weak spots:
- Already-revealed public keys: Coins held in address types/usage patterns where the public key is exposed on-chain could be more vulnerable if a capable quantum attacker existed; estimates discussed put this exposure around ~6.7M BTC under certain models.
- Transaction “window of exposure”: After broadcast and before confirmation, a public key may be observable. A sufficiently powerful attacker could theoretically derive a key and attempt to redirect funds before inclusion in a block (a race against confirmation).
- Migration is feasible but operationally hard: Switching to post-quantum cryptography is technically possible, but execution is complex in a decentralized system without a central administrator.
- Governance and coordination are the bottleneck: A meaningful transition requires aligned changes across wallet software, exchanges, custodians, miners, and user behavior—adopted voluntarily through Bitcoin’s open governance process.
- Early mitigation pathway exists: Work such as BIP 360 (quantum-resistant transaction formats) is referenced as an early starting point, not a complete end-to-end plan.
- Planning horizon resembles large infrastructure upgrades: Security specialists estimate a full ecosystem migration could take close to a decade, especially if it entails moving funds away from vulnerable address types and achieving broad adoption of new signature schemes.
- Why Y2K is an imperfect analogy: Y2K remediation was centralized and top-down; quantum migration changes underlying cryptographic assumptions and must be coordinated across a decentralized network.
- Broader cybersecurity implication (“Store Now, Decrypt Later”): Quantum risk is not limited to cryptoassets—banking, payments, authentication, and government communications face similar exposure if adversaries harvest encrypted data today for future decryption.
- Institutional signal to watch: Google targeting 2029 for internal PQC migration underscores long lead times and suggests ecosystem-level preparation needs to start well before market prices reflect the threat.
📘 Glossary
- ECC (Elliptic Curve Cryptography): A public-key cryptography family used by Bitcoin for signatures; secure under classical computing assumptions but vulnerable to sufficiently powerful quantum attacks.
- Public Key / Private Key: The public key can be shared and is used to verify signatures; the private key must remain secret and authorizes spending. Deriving the private key from the public key should be infeasible under normal conditions.
- Post-Quantum Cryptography (PQC): Cryptographic algorithms designed to remain secure even against attackers with quantum computers.
- Quantum Adversary: An attacker assumed to have access to large-scale, fault-tolerant quantum hardware capable of running cryptanalytic algorithms effectively.
- Error Correction (Quantum): Techniques that stabilize fragile quantum states; major determinant of whether quantum computers can scale to cryptographically relevant sizes.
- Transaction Window of Exposure: The time between a transaction being broadcast and its confirmation, during which relevant data (including a public key in common spending flows) may be observable.
- Confirmation: Inclusion of a transaction in a mined block (and subsequent blocks), which reduces the feasibility of transaction replacement or rerouting attempts.
- BIP (Bitcoin Improvement Proposal): A formal proposal process for changes and standards in Bitcoin; adoption requires broad voluntary consensus across the ecosystem.
- Store Now, Decrypt Later: A strategy where adversaries collect encrypted information today with the expectation that future advances (e.g., quantum computing) will enable decryption.
- Decentralized Governance: Bitcoin’s change process where no single party can mandate upgrades; coordination occurs through community review, implementation, and voluntary adoption.




















Comment 0